Libxslt Unmaintained with Critical Security Flaws: Strategic Risks and Remedies for 2025
In 2025, the widespread XML transformation library Libxslt finds itself at a critical inflection point. Despite its pervasive use across major content management systems, enterprise software, and web...
In 2025, the widespread XML transformation library
Libxslt
finds itself at a critical inflection point. Despite its pervasive use across major content management systems, enterprise software, and web platforms, Libxslt is currently
unmaintained
and burdened with
five known critical security vulnerabilities
, including remote code execution risks. Major technology companies such as Apple and Google have proposed patches, yet the absence of an active maintainer has stalled all official fixes. This situation exposes millions of systems to escalating security threats and highlights urgent challenges in open-source project governance, software supply chain security, and enterprise risk management.
Strategic Business Implications of Libxslt’s Maintenance Crisis
The unmaintained status of Libxslt has immediate and far-reaching consequences for businesses and technology leaders responsible for securing their software infrastructure:
- Heightened Security Risk: With publicly disclosed vulnerabilities—including remote code execution vectors—unpatched, organizations face increased exposure to cyberattacks that could compromise sensitive data, disrupt services, or facilitate persistent breaches.
- Compliance and Regulatory Pressure: Industries bound by data protection and operational integrity regulations must demonstrate effective patch management. Reliance on vulnerable, unmaintained libraries challenges compliance frameworks and invites potential penalties.
- Vendor and Ecosystem Fragmentation: Cloud providers, CMS vendors, and enterprise software suppliers must decide whether to adopt interim fixes, fork the library, or advise customers to migrate—decisions that could fracture ecosystem compatibility and complicate future support.
For decision-makers, the Libxslt scenario exemplifies the broader
open-source maintenance crisis
in 2025, underscoring the need for proactive governance and strategic dependency management.
Technical Risks and Vulnerability Landscape
Libxslt’s vulnerabilities, classified as critical CVEs, primarily enable remote code execution by processing crafted XML inputs. This threat vector jeopardizes any system that parses XML data using Libxslt, including:
- Popular CMS platforms such as WordPress and Drupal
- Enterprise document management and image gallery solutions
- Web servers and middleware components relying on XML transformations
Since the departure of the last official maintainer, no security patches have been merged into the project repository. Despite patch submissions from engineers at Apple and Google, the absence of a gatekeeper means these fixes remain dormant, leaving the vulnerabilities open to exploitation. The latest official release, version 1.1.9, does not incorporate these critical security updates.
This technical stagnation presents a sharp contrast to the rapid evolution in AI-powered vulnerability detection. Cutting-edge
With These
Features - AI2Work Analysis">Models With
These Features - AI2Work Analysis">AI models
like
GPT-4o
and
Claude 3.5 Sonnet
excel at flagging such security risks during code reviews but cannot substitute for active maintenance and patch deployment.
Broader Industry Trends Reflected by Libxslt’s Status
The Libxslt predicament is emblematic of two converging 2025 trends reshaping software development and security:
- Open-Source Project Sustainability Crisis: Critical software components increasingly suffer from abandonment as maintainers move on and funding remains scarce. This threatens foundational infrastructure that underpins countless products and services.
- Software Supply Chain Security Scrutiny: Enterprises are intensifying audits of third-party dependencies, with regulatory bodies and internal security teams demanding transparency and accountability for patching and risk mitigation.
Moreover, the community is witnessing a rise in forking efforts and alternative library development as stopgap solutions. However, these efforts risk ecosystem fragmentation, compatibility challenges, and duplicated effort if not coordinated effectively.
Practical Mitigation and Implementation Strategies for Enterprises
For organizations currently dependent on Libxslt, immediate and strategic actions are imperative to reduce exposure and prepare for longer-term solutions:
- Comprehensive Dependency Audits: Identify all systems and applications utilizing Libxslt. This includes direct usage and indirect dependencies embedded in CMS, middleware, and enterprise software stacks.
- Cautious Application of Unofficial Patches: While official fixes are stalled, vetted patches from trusted forks or contributions by major tech companies can serve as interim measures. Enterprises should validate these patches through rigorous testing.
- Sandboxing and Isolation: Implement runtime isolation and sandboxing for components handling XML data to mitigate potential exploit impact.
- Migration Planning: Evaluate alternative, actively maintained XML transformation libraries. Early migration planning reduces technical debt and aligns with future-proofing strategies.
- Integration of AI-Enabled Security Tools: Deploy AI-based static and dynamic code analysis platforms powered by GPT-4o or Claude 3.5 to proactively detect vulnerabilities in dependencies and custom implementations.
- Engagement with Open-Source Governance Bodies: Advocate for stewardship transfer or new maintainer recruitment through foundations like GNOME or corporate sponsorship initiatives to reestablish active maintenance.
Financial and Operational Impact Assessment
Failing to address Libxslt’s vulnerabilities translates into tangible financial and operational risks:
- Incident Response Costs: Exploited vulnerabilities can lead to costly incident response, forensic investigations, and remediation efforts.
- Reputational Damage: Data breaches and service outages erode customer trust and brand equity, with long-term revenue implications.
- Compliance Penalties: Non-compliance with industry regulations due to unpatched vulnerabilities can result in fines and legal consequences.
- Migration and Engineering Resource Allocation: Transitioning away from Libxslt requires developer time, testing, and coordination, which may delay other strategic initiatives.
However, investing in proactive mitigation and maintenance advocacy can reduce unplanned costs and position organizations as leaders in software supply chain security—a differentiator in the competitive 2025 technology landscape.
Future Outlook: Governance, AI, and Ecosystem Evolution
Libxslt’s current state catalyzes critical conversations on how open-source projects can be sustainably maintained in 2025 and beyond:
- Emergence of New Governance Models: Foundations, consortia, and corporate coalitions are increasingly exploring funding mechanisms that ensure maintenance continuity for vital open-source components.
- AI-Augmented Maintenance Workflows: Advanced models like GPT-4o and Claude 3.5 are beginning to assist maintainers by automating vulnerability detection, suggesting patches, and even generating test cases, potentially reducing the human burden.
- Policy and Regulatory Evolution: Governments and industry bodies are contemplating mandates requiring demonstrable patch management and risk mitigation for open-source dependencies in critical infrastructure.
- Community-Driven Forks and Alternatives: In the absence of official stewardship, community or corporate forks may become the default path, although they bring challenges around fragmentation and support consistency.
These developments underscore the necessity for enterprises and vendors to actively engage with open-source ecosystems—not only as consumers but as contributors to governance and maintenance.
Actionable Recommendations for Technology Leaders
Given the immediate risks and strategic implications of Libxslt’s unmaintained status, IT and security leaders should prioritize the following:
- Initiate an urgent risk assessment focused on Libxslt usage across your technology portfolio.
- Deploy AI-powered vulnerability scanning tools leveraging GPT-4o or Claude 3.5 to enhance detection capabilities.
- Engage internal development and security teams to evaluate unofficial patches and sandboxing techniques as interim risk mitigations.
- Develop a migration roadmap toward actively maintained XML transformation libraries to reduce long-term dependency risk.
- Collaborate with open-source foundations or corporate sponsors to advocate for resuming maintenance or managing a community fork.
- Communicate transparently with stakeholders about the risks and mitigation plans to maintain trust and compliance.
Addressing the Libxslt maintenance crisis is not merely a technical imperative—it is a strategic business priority that will shape software supply chain resilience and security posture throughout 2025 and beyond.
Related Articles
World models could unlock the next revolution in artificial intelligence
Discover how world models are reshaping enterprise AI in 2026—boosting efficiency, revenue, and compliance through proactive simulation and physics‑aware reasoning.
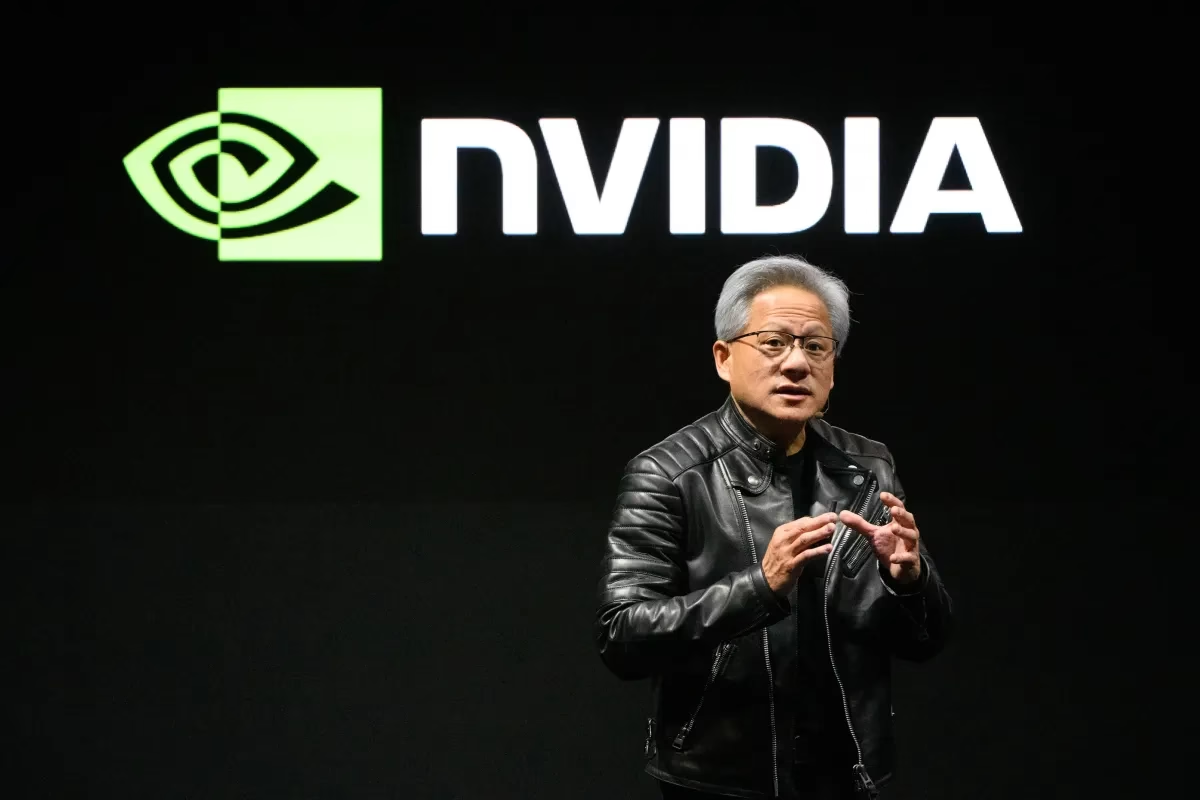
AI chip unicorns Etched.ai and Cerebras Systems get big funding boost to target Nvidia
Explore how AI inference silicon from Etched.ai and Cerebras is driving new capital flows, wafer‑scale performance, and strategic advantages for enterprises in 2026.
Nvidia's AI empire: A look at its top startup investments | TechCrunch
In 2026 Nvidia turns from GPU supplier into an integrated AI ecosystem architect. Explore its venture strategy, acquisitions like Groq, and the impact on the GPU ecosystem for enterprise leaders.