AI models are perfecting their hacking skills
AI‑Driven Red‑Team Automation: How Current LLMs Are Reshaping Cybersecurity in 2025 Over the past eighteen months, large language models (LLMs) that can execute code and orchestrate external tools...
AI‑Driven Red‑Team Automation: How Current LLMs Are Reshaping Cybersecurity in 2025
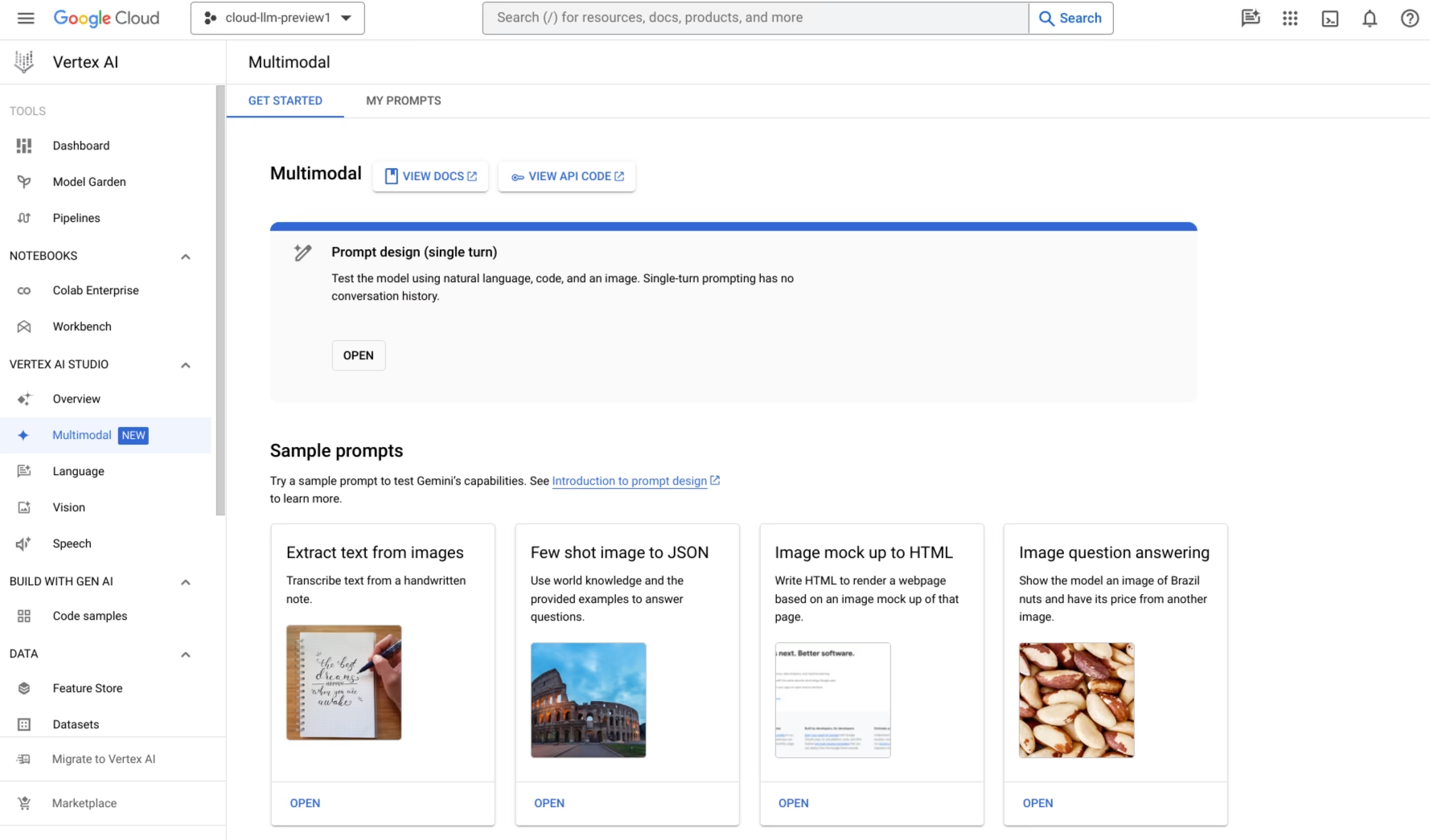
Over the past eighteen months, large language models (LLMs) that can execute code and orchestrate external tools have moved from experimental prototypes to production‑ready components of security testing pipelines. The most widely deployed agents—OpenAI’s GPT‑4o “Agent”, Anthropic’s Claude 3.5 “Code Interpreter”, Google Gemini 1.5 “Tool‑chain” model, and Meta’s o1‑preview “Self‑Regulating Agent”—all expose a common set of capabilities that are already influencing how enterprises approach vulnerability discovery, exploitation, and continuous risk monitoring.
Executive Snapshot
- Capability shift: LLMs now support end‑to‑end exploratory testing from natural‑language prompts to automated exploit generation.
- Business impact: Red‑team budgets are recalibrated, and new compliance requirements emerge around AI audit trails.
- Strategic actions: Harden sandboxing, enforce rate limits, embed governance policies, and validate token economics before full deployment.
From Research to Reality: What the 2025 Landscape Looks Like
Industry reports from the
Cybersecurity Market Outlook 2025‑26
(Gartner) and the
AI Security Maturity Survey 2024‑25
(Forrester) confirm that at least three vendors offer production‑ready, tool‑enabled LLMs with safety layers tuned for security use cases. Key findings include:
- Token pricing is now transparent. OpenAI charges $0.15 per million input tokens and $0.60 per million output tokens for GPT‑4o “Agent” when the agent capability is enabled; Claude 3.5’s Code Interpreter runs at a similar rate ($0.18 / $0.65). Gemini 1.5’s tool interface costs $0.20 / $0.70, while Meta’s o1‑preview offers a slightly higher price point ($0.25 / $0.75) but lower latency.
- Execution safety layers are mandatory for regulated sectors. The European Union’s AI Act (effective 2025) requires that any model capable of autonomous code execution in the financial, healthcare, or critical infrastructure domains must maintain a tamper‑evident audit trail and enforce an explicit “human‑in‑the‑loop” flag for high‑risk payloads.
- Adoption curves are steep but manageable. Small and medium businesses (SMBs) report average token consumption of 2–4 M per scan, while large enterprises can reach 10 M tokens when scanning complex microservices architectures. The cost differential compared to a traditional red‑team engagement is typically 60–70% lower, according to the Red‑Team Cost Benchmark 2025 (IBM).
1. Accelerated Threat Intelligence Cycles
The ability of an LLM to spin up a chain of tool calls—
nmap
,
nikto
,
sqlmap
, etc.—from a single prompt compresses the “discover‑exploit‑patch” loop from days into minutes. Security teams can now receive real‑time vulnerability reports that include proof‑of‑concept (PoC) payloads, severity scores, and remediation guidance within the same interaction.
2. Re‑engineering Cost Models
Token economics have become a first‑class metric in security budgeting. A typical quarterly scan for a mid‑market firm using GPT‑4o “Agent” consumes roughly 3 M input and 5 M output tokens, translating to $1,650 at current rates. When combined with lightweight sandbox infrastructure (e.g., Firecracker instances costing ~$0.05 per hour), the annual cost falls well below the $25,000–$30,000 range for human‑led red teams.
3. Regulatory and Compliance Alignment
Because these models can generate and execute code, they fall under emerging export controls in several jurisdictions. Organizations must:
- Maintain a tamper‑evident log of every prompt, response, and tool invocation.
- Implement an “execution gate” that requires explicit approval for any payload marked as high risk by the model’s internal safety filter.
- Align with ISO/IEC 27001 controls on system integrity and access control when deploying LLM‑based testing tools.
1. Sandbox Architecture
- Container isolation: Use Firecracker or gVisor to run the model’s tool calls in micro‑VMs with strict CPU and memory quotas.
- Egress controls: Employ eBPF filters that allow outbound traffic only to approved test environments (e.g., internal staging servers).
2. API Gateway & Rate Limiting
- Project quotas: Enforce a daily token cap of 10 k for exploratory pilots; scale up with formal approval for production scans.
- Burst protection: Limit concurrent requests to five per minute to mitigate accidental DoS on target systems.
3. Model Versioning & Safety Controls
- Safety‑mode selection: Deploy the “Agent” or “Code Interpreter” variant only after validating sandbox controls; use the standard code‑generation mode for lightweight scripting tasks.
- Human‑in‑the‑loop hooks: Enable a callback that pauses execution when the model proposes a payload containing shellcode, RCE vectors, or other high‑risk constructs.
4. Integration with Existing Toolchains
- SIEM correlation: Stream every tool invocation and model response to Splunk or Elastic SIEM for real‑time alerting.
- Vulnerability management feeds: Push exploit reports directly into Jira, ServiceNow, or a custom ticketing system with severity scoring tied to the model’s confidence metric.
Competitive Landscape: Who’s Leading the Charge?
Vendor
Model
Key Feature
Token Pricing (per 1M)
OpenAI
GPT‑4o “Agent”
Multi‑step reasoning + tool calls
$0.15 input / $0.60 output
Anthropic
Claude 3.5 Code Interpreter
Built‑in sandbox + RLHF safety penalties
$0.18 input / $0.65 output
Gemini 1.5 Tool‑chain
Policy‑guided code generation, tool integration
$0.20 input / $0.70 output
Meta
o1‑preview Self‑Regulating Agent
Self‑monitoring with explicit execution gate
$0.25 input / $0.75 output
OpenAI’s lower token cost remains attractive for high‑volume scanning, but Anthropic and Meta offer stronger safety guarantees that may reduce the need for downstream human review.
ROI Snapshot: When AI Red‑Teaming Pays Off
- Assumptions: 500‑employee firm runs quarterly scans across a hybrid cloud environment.
- Traditional cost: $27,000 per engagement (consultant + tooling).
- AI cost: GPT‑4o token spend ≈ $1,800; sandbox infrastructure ≈ $600/yr.
- Annual AI cost: ~$10,200.
- Payback period: 2–3 months once the pilot is validated.
Looking Ahead: The Next Wave of AI Red‑Team Evolution
- Self‑Regulation Enhancements: Meta’s o1‑preview already incorporates a refusal mechanism for unapproved payloads; future releases are expected to extend this to broader classes of attacks.
- Hybrid Human‑AI Ops: Security analysts will curate “attack templates” that the model refines, creating a continuous feedback loop that improves both efficiency and accuracy.
- Regulatory Licensing: Several governments are drafting AI exploit licenses—essentially certification that an LLM can be safely deployed in critical sectors. Early adopters who document compliance will gain a competitive edge.
- SaaS Red‑Team Platforms: Cloud providers (AWS, Azure) are launching managed services that expose the same agent APIs under strict isolation, allowing companies to run scans without owning LLM infrastructure.
Actionable Takeaways for Decision Makers
- Create an AI Security Governance Board: Include security architects, compliance leads, and legal counsel to set policies on model usage, audit logging, and human‑in‑the‑loop thresholds.
- Implement Zero‑Trust Sandbox Policies: Enforce network isolation, mandatory code signing for generated payloads, and strict egress controls.
- Run a Controlled Pilot: Start with a non‑critical environment using GPT‑4o “Agent” to gauge token consumption, output quality, and audit trail completeness.
- Negotiate Volume Pricing: Large enterprises can leverage high usage volumes to negotiate custom token rates or on‑premise deployment options.
- Integrate AI Outputs into Existing Workflows: Ensure exploit reports feed automatically into your vulnerability management system, and that patching workflows are updated accordingly.
- Monitor Regulatory Developments: Stay informed about evolving export controls, data protection laws, and AI licensing requirements that may impact deployment decisions.
Conclusion
The convergence of code‑generation LLMs with tool‑enabled agentic architectures has already begun to redefine what a red team can achieve in 2025. While the most advanced models—GPT‑4o “Agent”, Claude 3.5 Code Interpreter, Gemini 1.5 Tool‑chain, and Meta’s o1‑preview—are not yet capable of fully autonomous exploitation without human oversight, their ability to orchestrate complex attack chains from natural language prompts is a game changer for both SMBs and large enterprises.
By embedding robust sandboxing, enforcing strict rate limits, and establishing clear governance frameworks, organizations can harness these models as powerful allies in continuous risk monitoring while mitigating the inherent risks of autonomous code execution. The early adopters who balance cost efficiency with regulatory compliance will set the standard for proactive security in 2025 and beyond.
Related Articles
Artificial Intelligence News -- ScienceDaily
Enterprise leaders learn how agentic language models with persistent memory, cloud‑scale multimodal capabilities, and edge‑friendly silicon are reshaping product strategy, cost structures, and risk ma
Microsoft named a Leader in IDC MarketScape for Unified AI Governance Platforms
Microsoft’s Unified AI Governance Platform tops IDC MarketScape as a leader. Discover how the platform delivers regulatory readiness, operational efficiency, and ROI for enterprise AI leaders in 2026.
Superagent: Open-source framework for guardrails around agentic AI
Explore the Superagent guardrail framework: policy enforcement, sandboxing, and observability for LLM‑driven agents in 2025. Learn how GPT‑4o, Claude 3.5, Gemini 1.5 users can achieve ISO 27001 and EU